Tech Terms
Web 3.0 — It’s complicated; but, you’re going to be hearing more about this and so here’s the best concise introduction I could find (5min 18sec).
Heads Up
This week I published an essay with The Hoover Institution/Lawfare Blog — The Business of Knowing: Private Market Data and Contemporary Intelligence (see the attached PDF below).
Bottom Line: Many U.S. federal agencies are purchasing private market data. This paper argues that U.S. government access to at least some private market data — and the limiting of foreign access to this same information — is essential for national security. It also argues, however, for a refined awareness that acknowledges the privacy we have already lost and that implements greater government oversight and accountability.
“The American people and their government leaders cannot avoid these realities. Instead, they must adapt to them by refining our institutions and the critical balance between liberty and security. These changes necessarily require uncomfortable choices that bring with them no ironclad assurances of safety. But while an evolution as discussed in this paper does not guarantee success, a lack of adaptation will guarantee failure.”
Space Is Heating Up
What’s New: Josh Rogin has an interesting editorial in the Washington Post, arguing the United States is already battling its adversaries in space every day.
Why This Matters: “While Washington officials and experts warn of the risks of an arms race in space, the United States’ adversaries are constantly conducting operations against U.S. satellites that skirt the line between intelligence operations and acts of war.”
Key Points:
-
Rogin cites a conversation with Gen. David Thompson, Space Force’s vice chief of space operations, who warned that China could soon become the dominant power in the dark domain.
“The threats are really growing and expanding every single day. And it’s really an evolution of activity that’s been happening for a long time,” says Thompson. “We’re really at a point now where there’s a whole host of ways that our space systems can be threatened … [the Chinese are] fielding operational systems at an incredible rate.”
-
Both Russia and China regularly target American satellites with cyber attacks, jammers, and even lasers.
Rogin reports, “In 2019, Russia deployed a small satellite into an orbit so close to a U.S. “national security satellite” that the U.S. government didn’t know whether it was attacking or not, Thompson said. Then, the Russian satellite backed away and conducted a weapons test. It released a small target and then shot it with a projectile.”
-
This summer, the RAND Corporation issued a study on how to deter China in space that included the following findings:
-
“Because of China’s ambitions in space, deterring them requires the imposition of significant costs for aggressive action in space. Imposing political costs on China for aggressive action can be bolstered through strategic coordination between the United States and its allies.”
-
“China’s view of space as a critical U.S. vulnerability makes U.S. space capabilities attractive targets for attack. Highlighting China’s own reliance on space-based capabilities should be a part of a tailored deterrence strategy.”
-
What I’m Thinking:
-
Space security is only growing in importance. The national security equities in space are clear — without our off-planet assets, virtually none of our military capabilities, from submarines to fighter jets, will know who, when, where, or how to operate. But space is equally important economically, as commercial applications come online and proliferate. In 2019, one report said global space activity was more than $414.8 billion, with commercial space constituting 79% of total activity. This means space is yet another domain where government and industry interests are intermingled and will require strong cooperation to secure.
Cyber Spillover Between Iran and Israel
What’s New: Online hostilities between Iran and Israel are expanding into civilian targets.
Why This Matters: As the two nations square off in cyberspace, the threat of escalation and unintended consequences is rising.
Key Points:
-
Jerusalem and Tehran have been in “persistent cyber engagement” for years, but recent developments are bringing this shadow war into the light.
-
Last week, Fars News — a media outlet run by Iran’s Islamic Revolutionary Guard Corps (IRCG) — published the name, image, birthdate, email, social media handles, phone number, and home address of an Israeli security expert they accused of specializing in anti-Iran hacking operations.
-
This doxing1 was proceeded by an attack carried out last month by the Iranian hacking group, Black Shadow, who shut down a number of Israeli websites and stole user data from the Israeli LGBT dating site, “Atraf.”
-
Also last month, Tehran accused Israel of conducting a cyberattack that shut down most of Iran’s gas stations for nearly two weeks.
-
Separate, but relatedly, U.S. authorities are warning that Iran continues to target U.S. critical infrastructure, including hospitals.
What I’m Thinking:
-
It’s all fun and games until somebody gets hurt. Most of this activity is pretty standard. That is not to say, though, that it isn’t important or risky. Cyber is an attractive means of attack because it has the veneer of deniability and because it offers the ability to inflict coercive pain on a target typically without the death and destruction that accompanies “kinetic” options. However, things can always go sideways and the current engagement tempo between these two nations could easily get out of hand, with implications well beyond their respective borders. I’m all for playing hardball, but it’s better for everyone if we keep the game between the lines.
“C” Speaks
What’s New: Richard Moore, Britain’s new Chief of the Secret Intelligence Service (MI6), recently spoke about human intelligence in the digital age.
Why This Matters: This is Moore’s first public speech as Chief of MI6, or “C,” and it is telling how much this speech focuses on technological disruption and China.
Key Points:
-
“…We live in a world transformed by digital connectivity, and stand on the cusp of revolutionary advances in technology which will affect the manner in which we live and work in ways we cannot fully foresee.”
-
“Others would speak to you about the benefits associated with these new discoveries… and they are myriad. But I am paid to look at the threat side of the ledger. MI6 deals with the world as it is, not as we would like it to be. And the ‘digital attack surface’ that criminals, terrorists and hostile states seek to exploit against us is growing exponentially.”
-
“According to some assessments, we may experience more technological progress in the next ten years than in the last century, with a disruptive impact equal to the industrial revolution. As a society, we have yet to fully internalise (sic) this stark fact and its potential impact on global geopolitics. But it is a white-hot focus for MI6.”
-
“The tectonic plates are shifting as China’s power, and its willingness to assert it, grows … The Chinese Intelligence Services are highly capable and continue to conduct large scale espionage operations against the UK and our allies. This includes targeting those working in government, industries, or on research of particular interest to the Chinese state.”
-
“Adapting to a world affected by the rise of China is the single greatest priority for MI6. We are deepening our understanding of China across the UK intelligence community, and widening the options available to the government in managing the systemic challenges that it poses.”
-
“Our adversaries are pouring money and ambition into mastering artificial intelligence, quantum computing and synthetic biology, because they know that mastering these technologies will give them leverage. An intelligence service needs to be at the vanguard of what is technologically possible.”
-
“We can not match the scale and resources of the global tech industry, so we shouldn’t try. Instead we should seek their help … I cannot stress enough what a sea-change this is in MI6’s culture, ethos and way of working … We must become more open, to stay secret.”
What I’m Thinking:
-
Moore is right. Glad to see these views taking hold in places where it really matters.
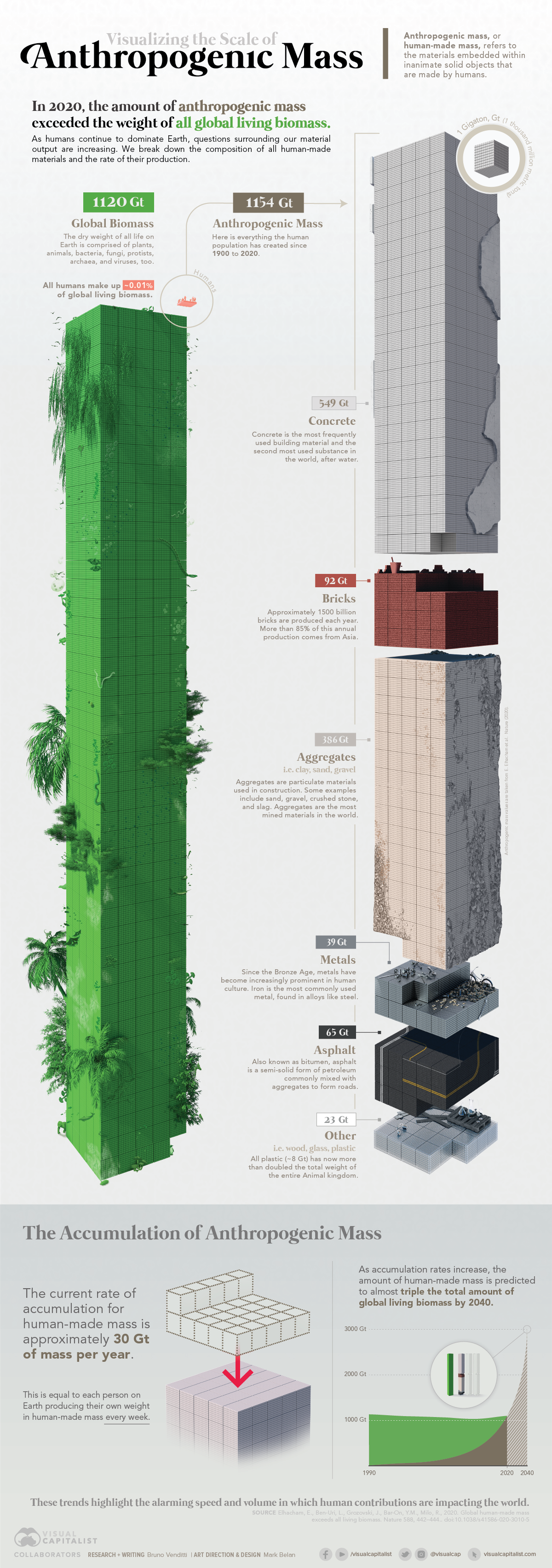
Let’s Get Visual
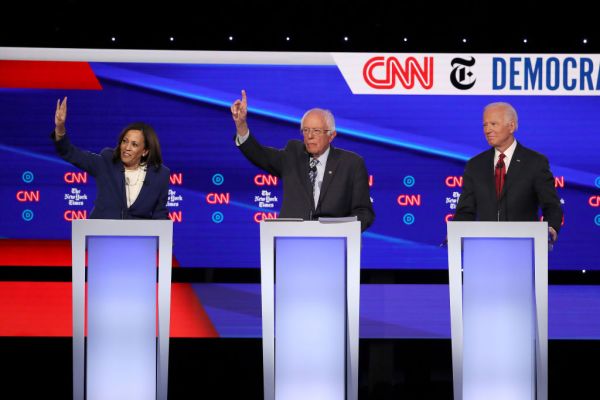
Nerd Humor

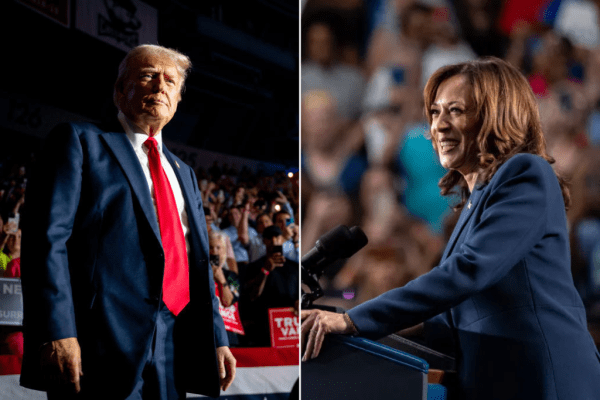
Quick Clicks
That’s it for this Friday Brief. Thanks for reading, and if you think someone else would like this newsletter, please share it with your friends and followers. Have a great weekend!






Please note that we at The Dispatch hold ourselves, our work, and our commenters to a higher standard than other places on the internet. We welcome comments that foster genuine debate or discussion—including comments critical of us or our work—but responses that include ad hominem attacks on fellow Dispatch members or are intended to stoke fear and anger may be moderated.